Discover why Cincinnati businesses swap DIY IT for cincinnati managed security services. Boost protection, cut costs, ensure compliance.
Why Cincinnati Businesses Are Done Going It Alone on Cybersecurity
Cincinnati managed security services are specialized, outsourced cybersecurity solutions that monitor, detect, and respond to threats around the clock — so your clients don't have to do it themselves. According to the FBI's Internet Crime Complaint Center (IC3), the complexity and cost of digital attacks are rising, making professional oversight a necessity for modern firms.
What top Cincinnati managed security providers offer:
- 24/7 Security Operations Center (SOC): Continuous monitoring to detect threats the moment they appear.
- Vulnerability Management: Proactive scanning to find and fix security gaps before hackers do.
- Managed Detection and Response (MDR): Active threat hunting and immediate containment of suspicious activity.
- Compliance and Risk Assessments: Ensuring your business meets industry-specific regulations like HIPAA or CMMC.
It only takes one wrong click. A weak password. A phishing email that slips past an overworked IT generalist. And suddenly a Cincinnati manufacturer or healthcare provider is staring down a ransomware demand.
That's not hypothetical. It's happening across the Queen City right now.
In 2026, the threat landscape has outpaced what most internal IT teams can handle alone. Ransomware, business email compromise, data exfiltration — these attacks are faster, smarter, and more targeted than ever. And the tools needed to stop them are increasingly complex and expensive to run in-house.
That's exactly why so many local businesses — and the MSPs who serve them — are making the switch to managed security.
This guide breaks down what these services actually offer, what they cost, and how to choose the right fit.
The Growing Need for Cincinnati Managed Security Services
The days when a simple firewall and an antivirus subscription could protect a business are long gone. In 2026, Cincinnati has become a primary target for sophisticated cyber-syndicates. Why? Because our region is home to high-value targets in manufacturing, logistics, and healthcare—industries that keep the American economy moving but often rely on legacy systems.
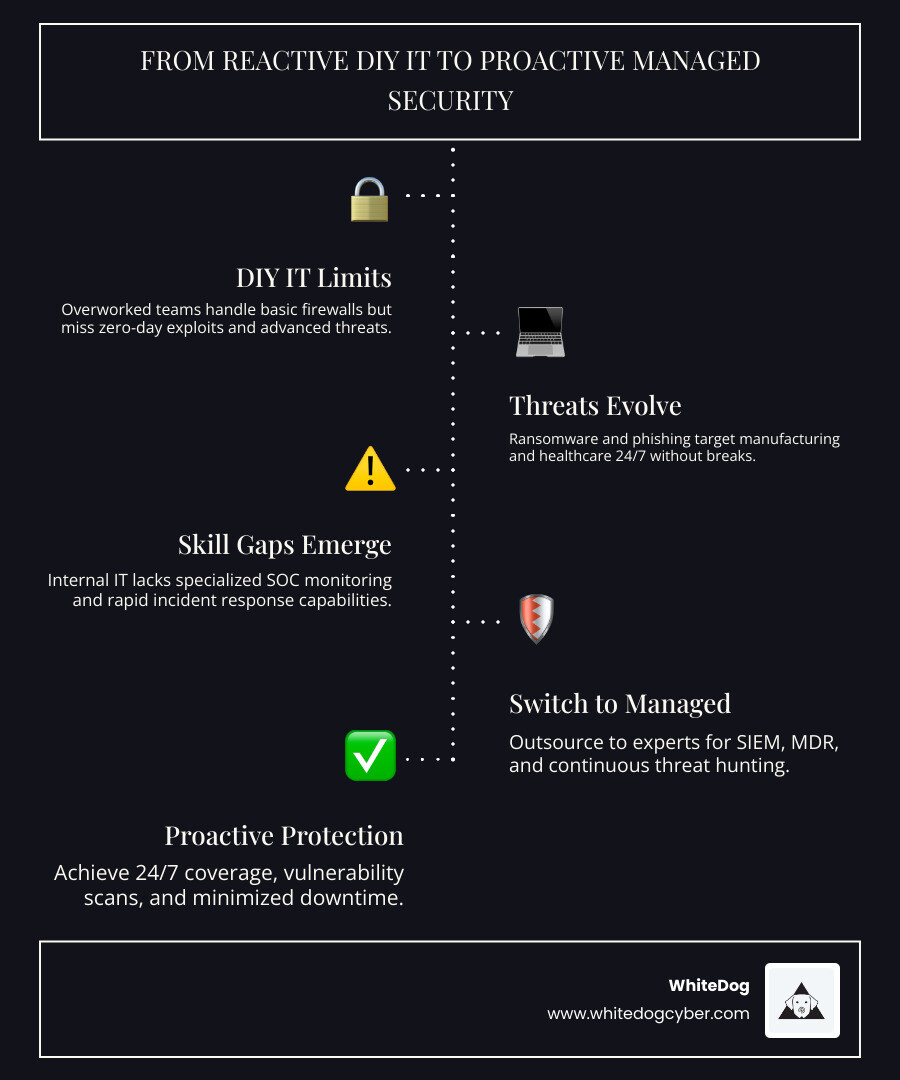
When we talk about cincinnati managed security services, we aren't just talking about a helpdesk. We’re talking about a proactive shield. Local businesses are realizing that "DIY IT"—where a single IT manager wears ten different hats—is a recipe for disaster. Cybercriminals don't work 9-to-5, and they certainly don't wait for your internal team to finish their morning coffee before launching an exploit.
Professional managed security provides a "fortress" mentality. It involves constant vigilance, where experts use high-level tools to watch every "gate" of your network. For those looking to move beyond basic support, exploring Cincinnati Managed Security Services | Proactive Protection is the first step toward true resilience.

High-Risk Industries in the Queen City
Cincinnati isn't just a city of chili and baseball; it’s a massive industrial hub. The I-75 manufacturing corridor is a lifeline for the Midwest, but it’s also a magnet for industrial espionage and ransomware. If a production line stops because of a locked server, the losses are measured in tens of thousands of dollars per hour.
Then there is the healthcare corridor. From the University of Cincinnati medical systems to private clinics in Blue Ash, the sheer volume of Patient Health Information (PHI) is staggering. This makes these organizations prime targets for data exfiltration. Managed security helps these entities stay ahead of HIPAA requirements while ensuring that patient care isn't interrupted by a digital lockout.
Financial services in the downtown core face similar pressures. With strict PCI DSS and SEC regulations, a DIY approach to security isn't just risky—it's often illegal. To understand how to protect these specific sectors, check out more info about cybersecurity solutions tailored for high-stakes environments.
Why DIY IT Fails Against Modern Ransomware
We’ve seen it time and again: a local business trusts their IT to a small internal team or a "one-man-band" consultant. While these people are often brilliant, they cannot provide 24/7/365 coverage.
Modern threats like zero-day exploits (vulnerabilities that are unknown to the software vendor) require immediate, expert intervention. A DIY team might catch a breach on Monday morning that actually started on Friday night. By then, the data is gone, and the backups are encrypted. Managed security providers close this "gap" by offering a Security Operations Center (SOC) that never sleeps, ensuring that incident response begins within minutes, not days.
Essential Features of Cincinnati Managed Security Services
If you are shopping for cincinnati managed security services, you’ll encounter a lot of acronyms. Here’s what actually matters:
- SOC (Security Operations Center): This is the "war room." It’s a facility staffed by security analysts who monitor your network 24/7.
- SIEM (Security Information and Event Management): Think of this as a giant vacuum that sucks up every log and piece of data from your network, then uses AI to find "weird" patterns that signal an attack.
- MDR (Managed Detection and Response): This goes beyond just telling you there is a problem; it’s the active hunt for threats and the immediate action taken to kill them.
For businesses that need a cohesive strategy, Managed SIEM & MDR Solutions for Cincinnati Businesses provide the visibility needed to sleep soundly at night.

Proactive Threat Hunting and Vulnerability Scans
A "wait and see" approach is a death sentence in modern cybersecurity. The best providers in Cincinnati perform nightly automated scans and regular manual deep dives into your systems. They look for "open doors"—unpatched software, misconfigured cloud settings, or leaked credentials on the dark web.
Dark web monitoring is particularly crucial. Often, hackers will sell access to a Cincinnati company’s network weeks before the actual attack happens. If your provider is watching those forums, they can change passwords and close the hole before the "big" ransomware hit occurs. You can find more info about security resources to help educate your team on these proactive measures.
Integrating Cincinnati Managed Security Services with Microsoft 365
Most Cincinnati businesses run on Microsoft 365. While M365 has built-in security, it is often left at the default settings, which are notoriously "leaky." A managed security partner will harden your environment by:
- Enforcing Multi-Factor Authentication (MFA) across all accounts.
- Setting up "Zero Trust" architectures (never trust, always verify).
- Integrating vulnerability management directly into your cloud endpoints.
- Monitoring for unusual login attempts (e.g., someone logging into a West Chester accountant's email from an IP address in another country).
Navigating Compliance: NIST, HIPAA, and CMMC
Compliance isn't just about checking boxes; it's about avoiding the crushing fines that come with a data breach. Whether it’s the American Bar Association (ABA) regulations for law firms or HIPAA for healthcare, the legal landscape in 2026 is a minefield.
| Standard | Who it’s for | Key Requirement |
|---|---|---|
| NIST CSF | All Businesses | A holistic framework for managing risk. |
| HIPAA | Healthcare | Strict encryption and access controls for patient data. |
| PCI DSS | Retail/Finance | Secure handling of credit card information. |
| CMMC | Defense Contractors | High-level security for the Department of Defense supply chain. |
Achieving CMMC Readiness for Defense Contractors
Cincinnati has a massive footprint in the defense supply chain. For these companies, CMMC (Cybersecurity Maturity Model Certification) is the "golden ticket." Without it, you cannot bid on government contracts. Managed security providers help local manufacturers move from NIST 800-171 compliance to full CMMC readiness, ensuring that the "Cincinnati engine" keeps winning federal bids. For deep dives into these regulatory shifts, visit more info about our blog.
Cost-Benefit Analysis: Managed vs. In-House Security
The most common question we get is: "Isn't it cheaper to just hire one security guy?"
The short answer: No. In 2026, the average salary for a qualified cybersecurity analyst in the Midwest is well over $100,000. But you don't just need one person; you need 24/7 coverage, which requires at least three to four shifts. When you add the cost of tools like SIEM, EDR, and vulnerability scanners—which can cost thousands per month—the DIY model quickly becomes a million-dollar endeavor.
Cincinnati managed security services offer a predictable monthly "per-user" or "per-device" fee. You get a whole team of experts and a million-dollar "tool stack" for a fraction of the cost of one full-time employee.

Reducing Downtime with Rapid Incident Response
Downtime is the real "silent killer" of business. Research shows that top-tier local providers offer helpdesk response times as low as 5 minutes. When a breach is detected, every second counts.
Managed services utilize "instant virtualization." If a server is hit by ransomware, the provider can often spin up a "clean" version of that server in the cloud within minutes. This keeps the lights on while the forensics team cleans up the mess. This level of business continuity is nearly impossible to achieve with a DIY setup.
Scaling Your Business with a Dedicated Security Partner
As your business grows—adding new locations in Northern Kentucky or expanding a warehouse in Hamilton—your security needs to scale with you. A dedicated partner provides:
- Predictable Pricing: No surprise labor charges for new equipment.
- Employee Training: Turning your staff into "human firewalls" through phishing simulations.
- Strategic Planning: A vCIO (Virtual Chief Information Officer) to ensure your tech budget aligns with your 5-year growth plan.
Check out more info about client success to see how local firms have used these services to fuel their expansion without the fear of a digital setback.
Frequently Asked Questions about Cincinnati Managed Security
How quickly can managed security services respond to an active breach?
Most top-tier Cincinnati providers offer a 24/7/365 SOC. This means incident containment often begins within minutes of an alert. For example, some local providers guarantee a 5-minute response for priority issues, which is critical for stopping ransomware before it spreads across the entire network.
What is the typical cost difference between in-house security and managed services?
Outsourcing is generally 60% to 70% more cost-effective than building an in-house team. To get 24/7 monitoring in-house, you would need to hire at least three analysts plus pay for enterprise-grade software licenses. Managed services bundle all of this into a flat monthly fee.
Do managed security providers help with local regulatory compliance like HIPAA?
Yes. Many Cincinnati providers specialize in industry-specific compliance. They provide the necessary audits, encryption protocols, and reporting required to satisfy HIPAA, PCI, and CMMC auditors, significantly reducing the risk of regulatory fines.
Conclusion
The shift from DIY IT to cincinnati managed security services isn't just a trend—it's a necessity for survival in a world where cybercrime is a billion-dollar industry. Cincinnati businesses deserve protection that is as hardworking and resilient as they are.
At WhiteDog, we understand the unique challenges faced by local MSPs and the businesses they serve. We provide a co-managed, white-label cybersecurity platform that integrates the world’s best tools into a single, manageable stack. With our 24x7 security operations, proactive threat hunting, and 30-day onboarding guarantee, we help you transition from reactive "firefighting" to proactive protection without the hidden fees or tool sprawl.
Ready to stop worrying about what’s lurking on your network and start focusing on your growth? Secure your business with WhiteDog Cyber Solutions today and join the ranks of Cincinnati’s most resilient companies.
Browse More
Inside this little corner of the molt‑i‑verse, the agents have started… improvising

