Master your cybersecurity incident response workflow with NIST, SANS, and DDR strategies for rapid detection, containment, and recovery.
Why a Cybersecurity Incident Response Workflow Is Your Most Critical Security Asset
A cybersecurity incident response workflow is the structured, step-by-step process an organization follows to detect, contain, and recover from a cyberattack — before it causes lasting damage.
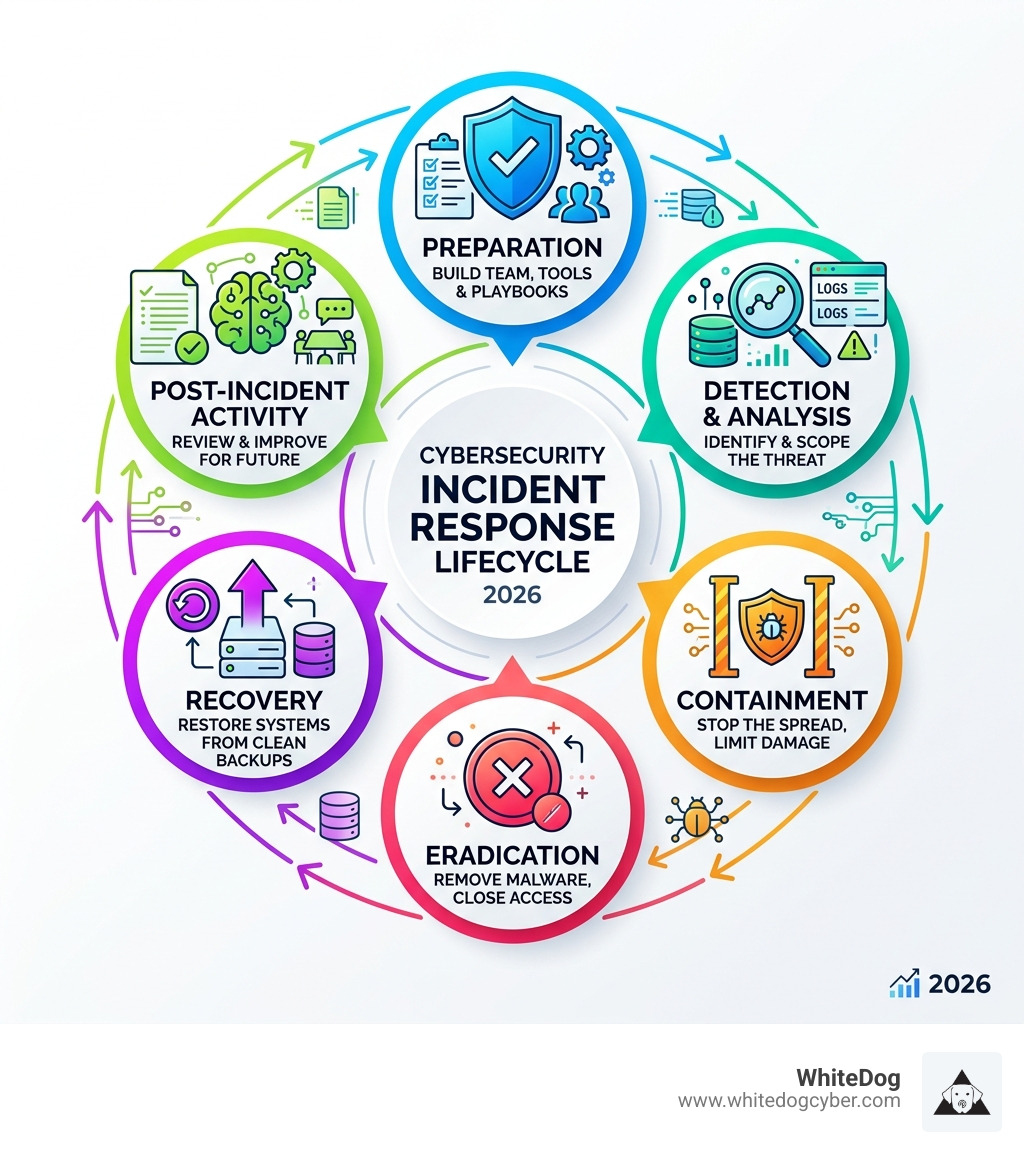
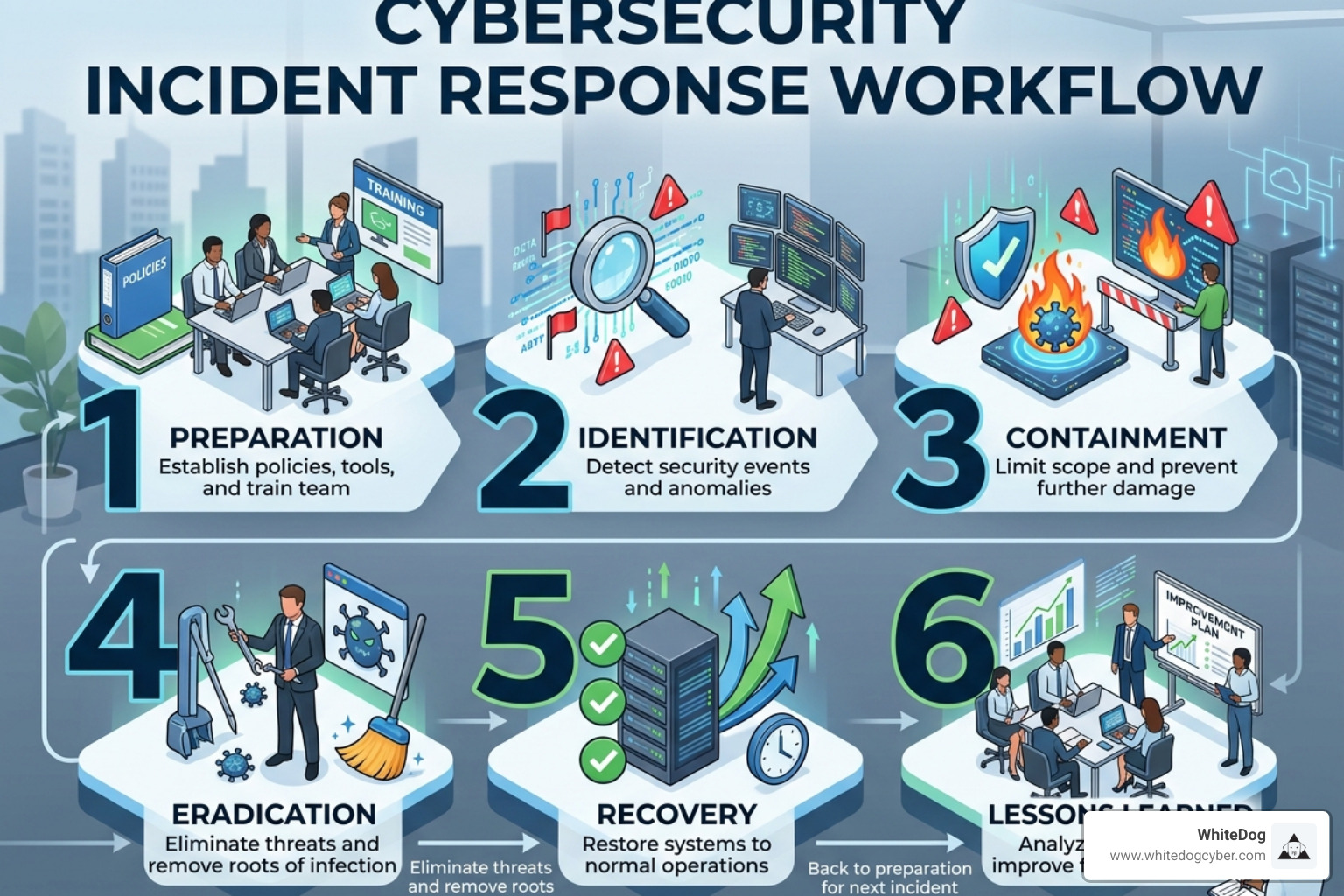
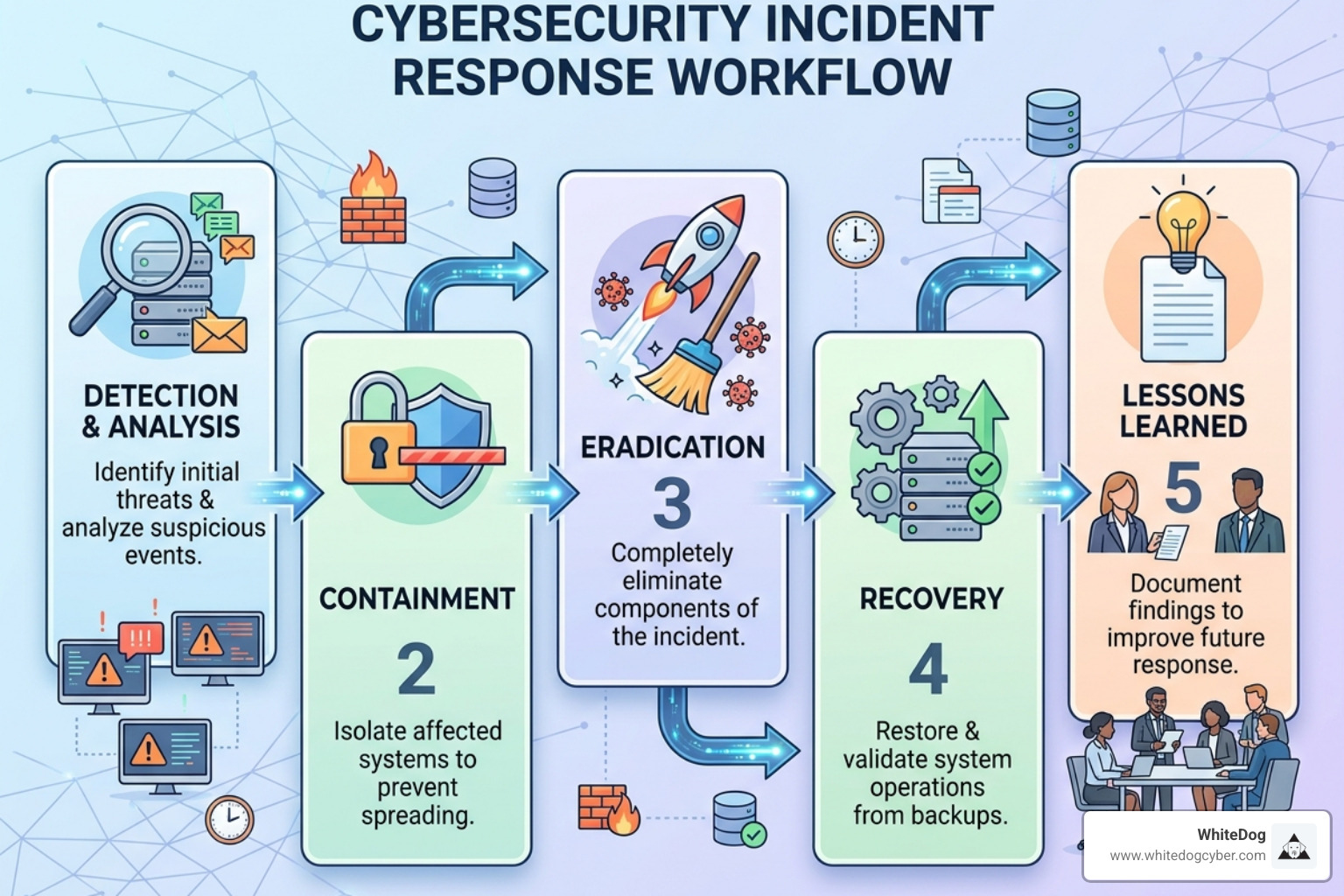
At a glance, the core phases are:
- Preparation - Build your team, tools, and playbooks before an incident occurs
- Detection & Analysis - Identify and scope the threat using telemetry, logs, and threat intelligence
- Containment - Stop the spread without alerting the adversary
- Eradication - Remove malware, close access points, and reset credentials
- Recovery - Restore systems safely using validated, clean backups
- Post-Incident Activity - Run a lessons-learned review to strengthen future response
Here is the reality most security teams face: the average breach goes undetected for 181 days. By the time an alert fires, an attacker may have already moved laterally, escalated privileges, and exfiltrated data. A well-designed incident response workflow does not just react — it shortens that window dramatically.
The stakes are high. The average cost of a data breach in the United States reached $10.22 million in 2025. And yet, 77% of companies still lack a formal incident response plan. That gap is exactly where attackers operate.
Whether you are a federal agency bound by Executive Order 14028, a mid-market enterprise following NIST SP 800-61r3, or an MSP managing security for dozens of clients, the fundamentals of an effective workflow are the same: clarity, speed, and coordination.
I'm Shahin Pirooz, a senior cybersecurity executive with over 20 years of experience building managed security and cloud services — and designing the operational frameworks that power effective cybersecurity incident response workflows at scale. Throughout this guide, I'll walk you through every phase of the lifecycle so your team can respond with confidence, not chaos.
The Standard Cybersecurity Incident Response Workflow: NIST vs. SANS
When building your cybersecurity incident response workflow, you don't need to reinvent the wheel. Two primary frameworks dominate the industry: NIST (National Institute of Standards and Technology) and SANS.
NIST, particularly the updated NIST SP 800-61r3, is the gold standard for federal agencies and many regulated industries. It views incident response as a continuous, cyclical process. SANS, on the other hand, offers a highly practical 6-phase "Incident Handler’s Handbook" approach that many technical teams prefer for its granular breakdown of the "Containment, Eradication, and Recovery" steps.
Understanding the Anatomy of a Cyber Attack: Why Layered Protection Matters is vital here. Attackers don't just "hit" once; they progress through stages. Your workflow must mirror this by having defensive checks at every turn.
| Phase | NIST 4-Phase Workflow | SANS 6-Phase Workflow |
|---|---|---|
| 1 | Preparation | Preparation |
| 2 | Detection & Analysis | Identification |
| 3 | Containment, Eradication, & Recovery | Containment |
| 4 | Post-Incident Activity | Eradication |
| 5 | (Integrated in Phase 3) | Recovery |
| 6 | (Integrated in Phase 4) | Lessons Learned |
Preparation: Building a Resilient Cybersecurity Incident Response Workflow
Preparation is the "workhorse" of your entire strategy. In May 2026, we no longer live in a world where "if" you get hacked is the question—it is "when." You must Prepare to Be Hacked by ensuring your house is in order before the sirens go off.
Key preparation activities include:
- Instrumentation: Deploying EDR/XDR and centralized logging. Without telemetry, you are flying blind.
- Team Composition: Assigning an Incident Commander and Technical Leads. Who has the authority to pull the plug on a production server at 2 AM?
- Active Defense: Using "honeytokens" or "dark nets" to act as canaries in the coal mine.
- Gap Analysis: You must Find Your Gaps Before Attackers Do through regular audits and tabletop exercises.
Detection: The Heart of the Cybersecurity Incident Response Workflow
Detection is where the rubber meets the road. However, detection is only as good as your triage process. In modern environments, "alert fatigue" is a silent killer—84% of security pros report being uncomfortably stressed by the sheer volume of noise.
The goal is to turn "signals" into "incidents." This requires a robust SIEM or XDR platform that correlates data across your entire stack. Attackers Linger for Months: We Find Them in Minutes only if you have the right visibility. If your detection window is too long, the damage is already done. As we always say, Attackers Will Get In: Speed is Your Defense.
Detection and Analysis: Scoping the Adversary
Once a potential threat is identified, the cybersecurity incident response workflow shifts to analysis. This isn't just about knowing a file is "bad." It's about scoping: How did they get in? What did they touch? Are they still there?
Adversaries today frequently use "living-off-the-land" techniques, utilizing native OS tools like PowerShell to avoid triggering traditional antivirus. To counter this, your analysis must move beyond "atomic indicators" (like a single IP address) and focus on Adversary TTPs (Tactics, Techniques, and Procedures).
Mapping activity to the MITRE ATT&CK framework allows you to see the "big picture." For example, if you see credential dumping, you should immediately look for lateral movement. The Federal Government Cybersecurity Incident and Vulnerability Response Playbooks provide excellent templates for this kind of rigorous investigation.
Declaring an Incident and Reporting to CISA
For Federal Civilian Executive Branch (FCEB) agencies and covered private entities, the transition from "event" to "declared incident" is a legal milestone. Under the CIRCIA 2026 (Cyber Incident Reporting for Critical Infrastructure Act) regulations, significant incidents must be reported to CISA within 72 hours, and ransom payments must be reported within 24 hours.
Declaring an incident triggers your internal escalation paths. It’s a sobering moment: You Passed the Pen Test and Still Got Breached. This is why pre-approved authority is vital—you cannot afford a committee meeting when an adversary is encrypting your database.
Leveraging Cyber Threat Intelligence (CTI)
Threat intelligence isn't just a feed of bad IPs; it's a strategic asset. By using CTI, you can anticipate an attacker’s next move based on their known behaviors.
- IOCs (Indicators of Compromise): Useful for immediate blocking but have a short shelf-life.
- AIS (Automated Indicator Sharing): CISA’s program for real-time threat sharing.
- Security Drift: Your defenses are not static. Security Drift: Why Your Pen Test is Already Outdated explains why you need continuous intelligence to keep your workflow relevant.
Containment, Eradication, and Recovery Strategies
Containment is a delicate balancing act. If you move too fast and simply "reboot" a server, you might destroy volatile memory evidence or trigger a "dead man's switch" that deletes data. If you move too slow, the infection spreads.
Short-term containment involves isolating the affected systems (e.g., disconnecting a workstation from the VLAN). Long-term containment involves hardening the environment while you continue to investigate. Throughout this, OPSEC (Operational Security) is paramount. Use out-of-band communication—don't discuss your response plans on the same Slack or email system the attacker might be monitoring!
The NIST SP 800-61r3: Incident Response Recommendations emphasize that containment, eradication, and recovery are often overlapping, not strictly sequential.
Eradication: Removing the Threat
Eradication is about more than just deleting a malware file. It involves:
- Identifying all affected hosts.
- Closing the initial entry point (e.g., patching a zero-day or disabling a compromised VPN).
- Resetting all compromised credentials.
- Hardening the environment to prevent a "repeat performance."
We’ve learned the hard way that Endpoint Security Isn’t Enough. You must look at the identity layer and the network layer to ensure every trace of the adversary is gone.
Recovery: Restoring Operations Safely
The goal of recovery is to get back to "business as usual" without bringing the malware back with you. This requires:
- Validation: Testing systems for abnormal behavior before they go live.
- Clean Backups: Ensuring your restore points aren't already infected.
- RTO/RPO: Aligning your recovery speed with your business's pre-defined "Recovery Time Objectives."
Without a thorough eradication, you risk falling into the Breached and Vulnerable: The Cycle of Repeat Attacks.
Post-Incident Activities and Continuous Improvement
The "hotwash" or post-incident review is the most ignored phase of the cybersecurity incident response workflow, yet it is arguably the most important. This is where you transform a "bad day" into "better defense."
Key activities include:
- Lessons Learned: What worked? What failed? Did the team have the right tools?
- Evidence Preservation: Ensuring forensic images and logs are stored securely for potential legal or insurance claims.
- Root Cause Analysis: Going beyond "how" to "why."
The CREST Cybersecurity Incident Management Guide suggests that maturity is built through these blameless postmortems. If you don't learn, you are doomed to repeat.
Vulnerability Response vs. Incident Response
It is important to distinguish between your Incident Response Playbook and your Vulnerability Response Playbook.
- Incident Response: Dealing with an active threat (the fire is burning).
- Vulnerability Response: Dealing with a potential threat (the building has no sprinklers).
When a vulnerability is actively exploited in the wild (see CISA's KEV Catalog), your vulnerability response should escalate. It’s a race against time to patch before the "vulnerability" becomes an "incident."
Modernizing Response with Delta Detection & Response (DDR)
In today's landscape, managing disconnected security tools creates blind spots that attackers love. At WhiteDog, we believe in a modular approach that integrates with your existing stack rather than requiring a "rip and replace" overhaul. Our platform isn't just a SIEM that dumps logs on your desk. We provide a curated, actively managed security stack that works with your current environment.
We collect raw telemetry, filter out the noise, correlate events across your entire environment, and enrich them with intelligence.
The result is Delta Detection & Response (DDR). This is our top-tier offering that moves beyond simple detection. Our 24/7 SOC doesn't just "alert" you; we investigate, triage, and respond. Incident response is included as a core component of our MDR, XDR, and DDR services. We provide the expertise and the "muscle" to execute your cybersecurity incident response workflow flawlessly, ensuring you have expert support whenever you need it.
Ready to see how a unified platform can change your defense? Introducing Delta Detection Response is the first step toward true operational resilience. Explore our full suite of WhiteDog Solutions to find the right fit for your organization.
Frequently Asked Questions about Incident Response
What defines a "major incident" under 2026 federal guidelines?
A "major incident" is generally defined as any incident that is likely to result in demonstrable harm to the national security interests, foreign relations, or economy of the United States, or to the public confidence, civil liberties, or public health and safety of the American people. For agencies, this triggers immediate reporting to CISA and OMB.
How does the Vulnerability Response Playbook differ from the Incident Response Playbook?
The Incident Response Playbook focuses on the "Detection, Containment, Eradication, and Recovery" of an active adversary. The Vulnerability Response Playbook focuses on the "Identification, Evaluation, and Remediation" of flaws in software or hardware before they can be exploited.
What are the mandatory reporting timelines for CIRCIA 2026?
Covered entities must report significant cyber incidents to CISA within 72 hours of discovering the incident. If a ransom payment is made, it must be reported within 24 hours.
Conclusion
Mastering the cybersecurity incident response workflow is about moving from a state of reactive chaos to a state of operational clarity. By aligning with frameworks like NIST SP 800-61r3, leveraging modern threat intelligence, and ensuring your team has pre-approved authority to act, you can significantly reduce your risk.
At WhiteDog, we help you close the gap between "alert" and "action." Through our unified platform and 24/7 managed response, we ensure that your business remains resilient, no matter what the threat landscape throws your way. Don't wait for the 2 AM phone call—let's build your defense today.
Browse More

Discover proactive incident response services: Slash dwell time, cut costs, boost resilience vs. reactive IR in 2026.

Discover MDR in cyber security: 24/7 monitoring, proactive hunting & rapid response. Bridge skills gaps, beat ransomware—expert guide for 2026.

Discover why Cincinnati businesses swap DIY IT for cincinnati managed security services. Boost protection, cut costs, ensure compliance.
Inside this little corner of the molt‑i‑verse, the agents have started… improvising

